「Linux路由实践」之推动同网段主机间回环网口通信【主机路由篇】
电脑杂谈 发布时间:2020-03-14 02:02:44 来源:网络整理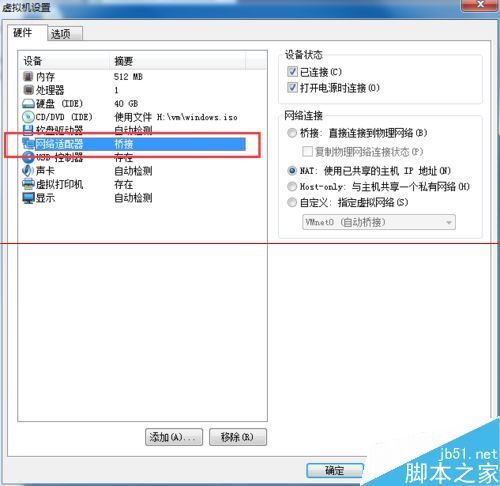
环境说明:
注:VMware Workstation 12 Pro是 VMware, Inc 的商业产品,点此下载试用版
我们开始吧~
1.我们先看一下主机的网络相关状况: 首先是route1:

[root@route1 ~]# ifconfig
eth1 Link encap:Ethernet HWaddr 00:0C:29:CC:99:C6
inet addr:192.168.10.100 Bcast:0.0.0.0 Mask:255.255.255.0
inet6 addr: fe80::20c:29ff:fecc:99c6/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:159 errors:0 dropped:0 overruns:0 frame:0
TX packets:132 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:18586 (18.1 KiB) TX bytes:21818 (21.3 KiB)
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:65536 Metric:1
RX packets:41 errors:0 dropped:0 overruns:0 frame:0
TX packets:41 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:3816 (3.7 KiB) TX bytes:3816 (3.7 KiB)
然后看一下route2:
[root@route2 ~]# ifconfig
ens37: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.10.200 netmask 255.255.255.0 broadcast 0.0.0.0
inet6 fe80::20c:29ff:fe27:2379 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:27:23:79 txqueuelen 1000 (Ethernet)
RX packets 94 bytes 9235 (9.0 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 112 bytes 22335 (21.8 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
lo: flags=73<UP,LOOPBACK,RUNNING> mtu 65536
inet 127.0.0.1 netmask 255.0.0.0
inet6 ::1 prefixlen 128 scopeid 0x10<host>
loop txqueuelen 1 (Local Loopback)
RX packets 12 bytes 1020 (1020.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 12 bytes 1020 (1020.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
我们提到,route1和route2的主网口在192.168.10.0/24网络中,这也正是我们推动回环网口互通的重点,后面会具体表述。

2.为了更好地呈现实验效果同网段活动主机同网段活动主机,分别自动设置一下route1和2的回环网口IP
root@route1 ~]# ifconfig lo 8.8.8.8/32 #之所以需要指定掩码为32是为了申明该网络只有自己一个地址 下同
[root@route1 ~]# ifconfig lo
lo Link encap:Local Loopback
inet addr:8.8.8.8 Mask:0.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:65536 Metric:1
RX packets:41 errors:0 dropped:0 overruns:0 frame:0
TX packets:41 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:3816 (3.7 KiB) TX bytes:3816 (3.7 KiB)
接着修改route2的lo回环网口:
[root@route2 ~]# ifconfig lo 8.8.8.9/32 #原因同上
[root@route2 ~]# ifconfig lo
lo: flags=73<UP,LOOPBACK,RUNNING> mtu 65536
inet 8.8.8.9 netmask 0.0.0.0
inet6 ::1 prefixlen 128 scopeid 0x10<host>
loop txqueuelen 1 (Local Loopback)
RX packets 12 bytes 1020 (1020.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 12 bytes 1020 (1020.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0

3.我们看一下路由信息
[root@route1 ~]# route -n Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Ifac e 192.168.10.0 0.0.0.0 255.255.255.0 U 0 0 0 eth1 [root@route2 ~]# route -n Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Ifac e 192.168.10.0 0.0.0.0 255.255.255.0 U 0 0 0 ens3 7
4.将对方主机的IP设为本机的默认路由这一步非常重要。我们先为route1添加路由信息:
[root@route1 ~]# route add -host 8.8.8.9 gw 192.168.10.200 [root@route1 ~]# route -n Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 8.8.8.9 192.168.10.200 255.255.255.255 UGH 0 0 0 eth1 192.168.10.0 0.0.0.0 255.255.255.0 U 0 0 0 eth1
接着为route2添加路由信息:
[root@route2 ~]# route add -host 8.8.8.8 gw 192.168.10.100 [root@route2 ~]# route -n Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Ifac e 8.8.8.8 192.168.10.100 255.255.255.255 UGH 0 0 0 ens3 7 192.168.10.0 0.0.0.0 255.255.255.0 U 0 0 0 ens3 7
5.OK,现在我们来验证一下前面的配置
[root@route1 ~]# yum -y install tcpdump #我们先在route1上安装抓包工具tcpdump [root@route2 ~]# ping -I 8.8.8.9 8.8.8.8 # 在route2上 通过PING测试并指定使用回环网卡 来测试和route1的连接性 PING 8.8.8.8 (8.8.8.8) from 8.8.8.9 : 56(84) bytes of data. 64 bytes from 8.8.8.8: icmp_seq=1 ttl=64 time=0.552 ms 64 bytes from 8.8.8.8: icmp_seq=2 ttl=64 time=0.421 ms 64 bytes from 8.8.8.8: icmp_seq=3 ttl=64 time=0.492 ms 64 bytes from 8.8.8.8: icmp_seq=4 ttl=64 time=0.515 ms
回到route1 我们看到
[root@route1 ~]# tcpdump -i eth1 icmp tcpdump: verbose output suppressed, use -v or -vv for full protocol decode listening on eth1, link-type EN10MB (Ethernet), capture size 65535 bytes 06:07:33.284722 IP 8.8.8.9 > 8.8.8.8: ICMP echo request, id 9629, seq 161, length 64 06:07:33.284774 IP 8.8.8.8 > 8.8.8.9: ICMP echo reply, id 9629, seq 161, length 64 06:07:34.286734 IP 8.8.8.9 > 8.8.8.8: ICMP echo request, id 9629, seq 162, length 64 06:07:34.286768 IP 8.8.8.8 > 8.8.8.9: ICMP echo reply, id 9629, seq 162, length 64 06:07:35.288463 IP 8.8.8.9 > 8.8.8.8: ICMP echo request, id 9629, seq 163, length 64 06:07:35.288495 IP 8.8.8.8 > 8.8.8.9: ICMP echo reply, id 9629, seq 163, length 64 06:07:36.290517 IP 8.8.8.9 > 8.8.8.8: ICMP echo request, id 9629, seq 164, length 64 06:07:36.290549 IP 8.8.8.8 > 8.8.8.9: ICMP echo reply, id 9629, seq 164, length 64 06:07:37.293046 IP 8.8.8.9 > 8.8.8.8: ICMP echo request, id 9629, seq 165, length 64 06:07:37.293104 IP 8.8.8.8 > 8.8.8.9: ICMP echo reply, id 9629, seq 165, length 64 06:07:38.294611 IP 8.8.8.9 > 8.8.8.8: ICMP echo request, id 9629, seq 166, length 64 06:07:38.294644 IP 8.8.8.8 > 8.8.8.9: ICMP echo reply, id 9629, seq 166, length 64 06:07:39.296849 IP 8.8.8.9 > 8.8.8.8: ICMP echo request, id 9629, seq 167, length 64 06:07:39.296882 IP 8.8.8.8 > 8.8.8.9: ICMP echo reply, id 9629, seq 167, length 64 06:07:40.299690 IP 8.8.8.9 > 8.8.8.8: ICMP echo request, id 9629, seq 168, length 64 06:07:40.299727 IP 8.8.8.8 > 8.8.8.9: ICMP echo reply, id 9629, seq 168, length 64 06:07:41.300620 IP 8.8.8.9 > 8.8.8.8: ICMP echo request, id 9629, seq 169, length 64
6.通过上述检测,可以确认连接性测试成功。
本文来自电脑杂谈,转载请注明本文网址:
http://www.pc-fly.com/a/tongxinshuyu/article-144074-1.html
相关阅读
发表评论 请自觉遵守互联网相关的政策法规,严禁发布、暴力、反动的言论
-

-
 刘东宇
刘东宇自创曲哦
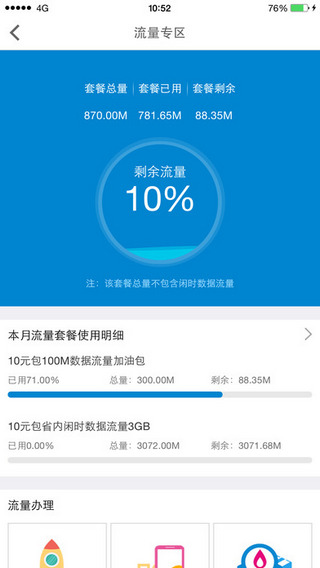 山东移动网上营业厅取消业务_中国移动网上营业厅_10086中国移动营业厅
山东移动网上营业厅取消业务_中国移动网上营业厅_10086中国移动营业厅 梦幻西游: 玩家每天两分钟在玩家的院子里种2颗和3颗,收获丰硕
梦幻西游: 玩家每天两分钟在玩家的院子里种2颗和3颗,收获丰硕 香港中文大学书的翻译
香港中文大学书的翻译 国家推广培训证书考试的主要内容
国家推广培训证书考试的主要内容
扶植此人推翻合法巴拿马政府做了总统