CA证书跟TLS介绍(2)
电脑杂谈 发布时间:2019-12-29 14:02:10 来源:网络整理创建CA服务器


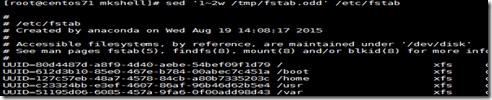
1.生成私钥文件 [root@yxh6 data]# (umask 077;openssl genrsa -out app.key 1024) Generating RSA private key, 1024 bit long modulus ..............................++++++ .....................++++++ e is 65537 (0x10001) [root@yxh6 data]# ls app.key 2.利用私钥文件生成申请文件 [root@yxh6 data]# openssl req -new -key app.key -out app.csr You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [XX]:CN State or Province Name (full name) []:beijing Locality Name (eg, city) [Default City]:beijing Organization Name (eg, company) [Default Company Ltd]:mage Organizational Unit Name (eg, section) []:M30 Common Name (eg, your name or your server's hostname) []:www.yxh.com Email Address []: Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []: An optional company name []: [root@yxh6 data]# ls app.csr app.key 3.将申请文件发送给CA scp app.csr 192.168.33.130:/etc/pki/CA 4.CA颁发证书 回到CA服务器执行颁发证书 touch index.txt echo 0F > serial [root@centos7 CA]# openssl ca -in app.csr -out certs/app.crt -days 100 Using configuration from /etc/pki/tls/openssl.cnf Check that the request matches the signature Signature ok Certificate Details: Serial Number: 15 (0xf) Validity Not Before: May 19 09:35:37 2018 GMT Not After : Aug 27 09:35:37 2018 GMT Subject: countryName = CN stateOrProvinceName = beijing organizationName = mage organizationalUnitName = M30 commonName = www.yxh.com X509v3 extensions: X509v3 Basic Constraints: CA:FALSE Netscape Comment: OpenSSL Generated Certificate X509v3 Subject Key Identifier: 71:DC:D4:AE:8A:5A:16:A4:13:62:D7:3A:C9:C7:DD:A7:9C:95:B0:4F X509v3 Authority Key Identifier: keyid:C6:80:BB:D0:7D:12:F4:EF:1A:69:CD:92:D3:F7:E1:3D:8A:27:CD:76 Certificate is to be certified until Aug 27 09:35:37 2018 GMT (100 days) Sign the certificate? [y/n]:y 1 out of 1 certificate requests certified, commit? [y/n]y Write out database with 1 new entries Data Base Updated [root@centos7 certs]# ls app.crt 5.证书发送客户端 scp app.csr 192.168.33.129:/data 客户端可以拿着这个证书在应用程序中使用
CA签发证书(客户端)
可以把证书cacert.pem下载至windows中进行可视化查看证书信息
需要.pem(cacert.pem)后缀名改成windows能辨识的.cer(cacert.cer)或者.crt 点击安装证书可以把此证书安装至可信任的证书路径中
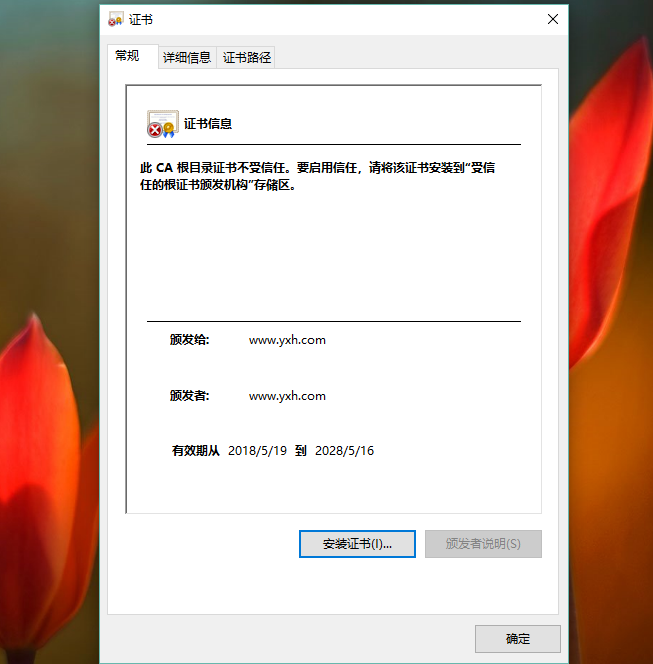
查看证书中的信息:
openssl x509 -in /PATH/FROM/CERT_FILE -noout -text|issuer|subject|serial|dates
openssl ca -status SERIAL 查看指定编号的证书状态
吊销证书
在客户端获取要注销的证书的serial
openssl x509 -in /PATH/FROM/CERT_FILE -noout -serial -subject
在CA上,根据顾客递交的serial与subject信息,对比检测是否与index.txt文件中的信息一致,吊 销证书:
openssl ca -revoke /etc/pki/CA/newcerts/SERIAL.pem
指定第一个注销证书的编号,注意:第一次更新证书注销列表前,才须要执行 echo 01 > /etc/pki/CA/crlnumber
更新证书注销列表 openssl ca -gencrl -out /etc/pki/CA/crl.pem
查看crl文件: openssl crl -in /etc/pki/CA/crl.pem -noout -text
ssh: secure shell, protocol, 22/tcp, 安全的远程登陆
两种形式的用户登入认证:
1.基于password
1.客户端向服务端发送SSH恳求
2.服务端收到恳求,发送私钥给客户端
3.客户端键入用户名跟密码通过私钥加密回传给服务端
4.服务端通过公钥揭秘得到用户名跟密码跟本地的用户名密码进行验证匹配
2.基于key
1.首先在客户端生成一对秘钥对
2.客户端将鉴权拷贝给服务端并重命名为 authorized_keys
3.客户端向服务端发送一个连结恳求,信息包括ip,用户名
4.服务端得到客户端消息后,会至authorized_keys查找是否有对应信息使得随机生成一个字符串
5.服务端把随机生成的字符串用客户端公钥加密发送给客户端

6.客户端接收至加密字符串后用自己的公钥对字符串进行揭秘,并且把揭秘后的字符串发送给服务端
7.服务端会把接收至的字符串跟其实自己生成的随机字符串进行验证匹配
ssh客户端:
1.客户端配置文件 /etc/ssh/ssh_config ssh服务端的配置文件 /etc/ssh/sshd_config
ssh客户端会在第一次连结的时侯把远程主机的私钥下载至本机,如果还要假扮其它早已连结过的主机,需要把对方的公钥拷贝至本地来
实现指定用户无密码连结,默认是root用户 在ssh-copy-id命令中指定特定的用户名都会把私钥文件拷贝至指定用户的家目录下
ssh-copy-id yxh@192.168.33.130


1.在客户端生成密钥对 [root@yxh6 data]# ssh-keygen -t rsa Generating public/private rsa key pair. Enter file in which to save the key (/root/.ssh/id_rsa): Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in /root/.ssh/id_rsa. Your public key has been saved in /root/.ssh/id_rsa.pub. The key fingerprint is: 84:69:ce:6b:19:1d:09::94:66:06:2e:76:57:8b:0b root@yxh6.localdomain The key's randomart image is: +--[ RSA 2048]----+ | .=+.. | | . ** o | | o E+* = | | . o * + . | | = S | | + | | + | | . | | | +-----------------+ [root@yxh6 data]# cd /root/.ssh [root@yxh6 .ssh]# ls id_rsa id_rsa.pub known_hosts 2.把公钥复制到服务端主机 [root@yxh6 .ssh]# ssh-copy-id 192.168.33.130 root@192.168.33.130's password: Now try logging into the machine, with "ssh '192.168.33.130'", and check in: .ssh/authorized_keys to make sure we haven't added extra keys that you weren't expecting. 3.直接连接远程主机 [root@yxh6 .ssh]# ssh 192.168.33.130 Last login: Sat May 19 17:31:50 2018 from 192.168.33.1 this is etc/motd,welcome.... [root@centos7 ~]#
View Code
多台主机之间实现互相key认证登陆
1.在一台主机A上生成一对秘钥对所有主机使用同一秘钥
2.ssh-copy-id A
3.scp -rp /root/.ssh B:/root
4.scp -rp /root/.ssh C:/root
expect匹配输出规则:
#Are you sure you want to continue connecting (yes/no)?
#root@192.168.33.129's password:


1 生成ip列表文件 2 [root@centos7 .ssh]# cat ip.txt 3 192.168.33.129 4 192.168.33.130 5 6 #!/bin/bash 7 rpm -q expect &> /dev/null || yum install -y expect 8 ssh-keygen -P "" -f "/root/.ssh/id_rsa" 9 password=root 10 while read ipaddr;do 11 echo $ipaddr 12 expect <<EOF 13 spawn ssh-copy-id $ipaddr 14 expect { 15 "yes/no" { send "yes\n";exp_continue } 16 "password:" { send "$password\n" } 17 } 18 expect eof 19 EOF 20 done < ip.txt 21 22 给脚本文件设置执行权限 23 chmod +x ssh_key.sh 24 25 执行脚本 26 ./ssh_key.sh
View Code
本文来自电脑杂谈,转载请注明本文网址:
http://www.pc-fly.com/a/jisuanjixue/article-135087-2.html
 awk数组_shell脚本数据类型_awk关联数组
awk数组_shell脚本数据类型_awk关联数组 Spring AOP,AspectJ, CGLIB 有点晕
Spring AOP,AspectJ, CGLIB 有点晕 字符串 从0到1:Python爬虫知识点梳理
字符串 从0到1:Python爬虫知识点梳理 成千上万的精品店再次升级,华为畅享7 Plus评测
成千上万的精品店再次升级,华为畅享7 Plus评测
说白了